Run Advanced Phishing Campaigns That Feel Real
Create realistic phishing simulations across email, smishing, quishing, and spear phishing workflows using custom templates, advanced landing pages, multi-step flows, and trackable interactions.
Modern phishing threats are more targeted, more varied, and more convincing than simple one-format simulations. Organizations need the ability to create phishing experiences that better reflect real attacker behavior in order to generate more meaningful awareness outcomes.
Advanced Phishing Campaigns give teams the flexibility to design simulations that go beyond basic email tests. Build custom content, define more realistic user journeys, and create multi-channel phishing scenarios that improve engagement, realism, and training relevance.
Simulate phishing scenarios across email, SMS-style flows, QR phishing, and targeted spear phishing experiences.
Create custom landing pages, staged interactions, and more advanced engagement paths that feel closer to real-world phishing attempts.
Track how users interact with different phishing formats and use those insights to improve training effectiveness over time.
Advanced campaigns support multiple phishing vectors so organizations can simulate different threat formats and improve awareness across more realistic scenarios.
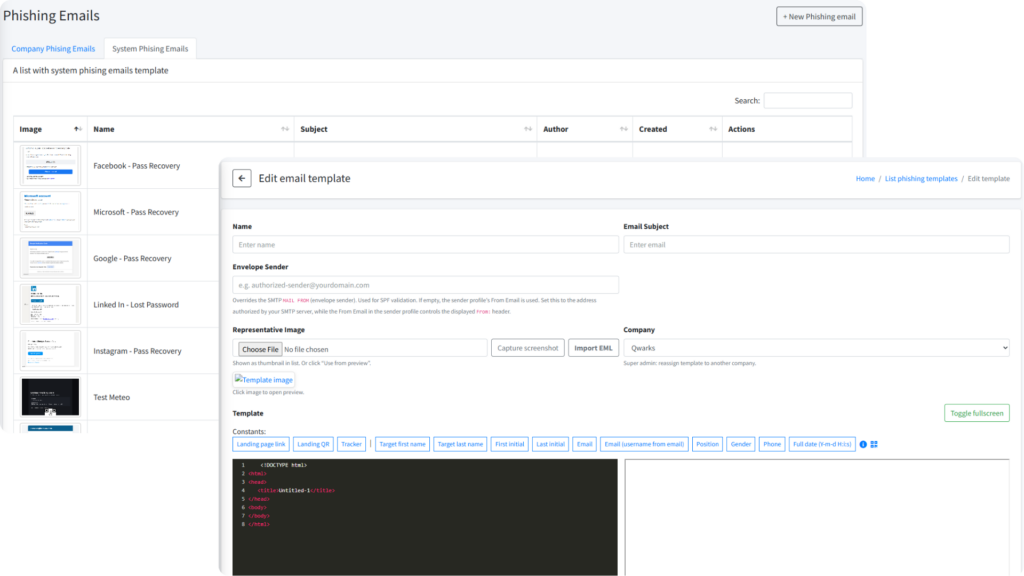
Launch realistic email simulations using prebuilt templates or fully custom HTML content.
Generate targeted, trackable phishing links quickly, with or without landing pages, for focused simulation workflows.
Create mobile-style phishing scenarios that reflect SMS-driven social engineering.
Simulate QR-code phishing paths that test how users respond to scan-based threats.
Launch realistic email simulations using prebuilt templates or fully custom HTML content.
Generate targeted, trackable phishing links quickly, with or without landing pages, for focused simulation workflows.
Create mobile-style phishing scenarios that reflect SMS-driven social engineering.
Simulate QR-code phishing paths that test how users respond to scan-based threats.
Yes. Discovery and monitoring are designed to work without endpoint agents for fast deployment.
Yes. Use built-in connectors, webhooks, and an API-first approach for routing.
Evidence-backed findings and scoring aligned to exposure, exploitability, and ownership signals.
Yes. Map checks to your internal thresholds and enforce policies across business units.