A platform built by security professional that aims to provide 100% operativity and visibility
We are a team of experienced security and development professionals dedicated to building practical, real-world tools. Simulated Security was born from a problem that had no existing solution.
Our mission is to create reliable, effective tools that address real security challenges, combining deep expertise with hands-on innovation.
Harnessing the power of an integrated operational platform designed to give visibility and real world attack scenarios
We are using real world scenarios and techniques. All simulations are based on real documented attacks from the past.
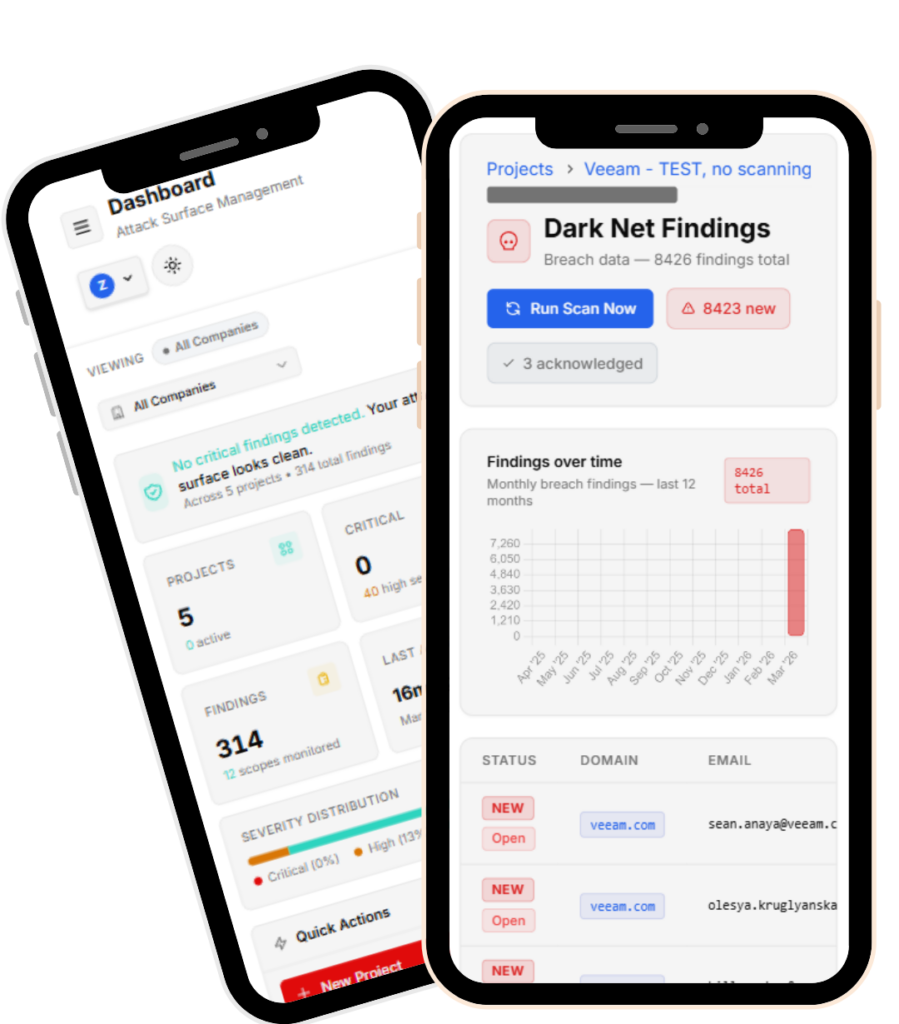
Evaluated digital assets, human assets and continuous monitor them. Increase resilience. Build security operations.
Designed with a clear set of goals. Not overlapping with other solutions but offering enough visibility and coverage.
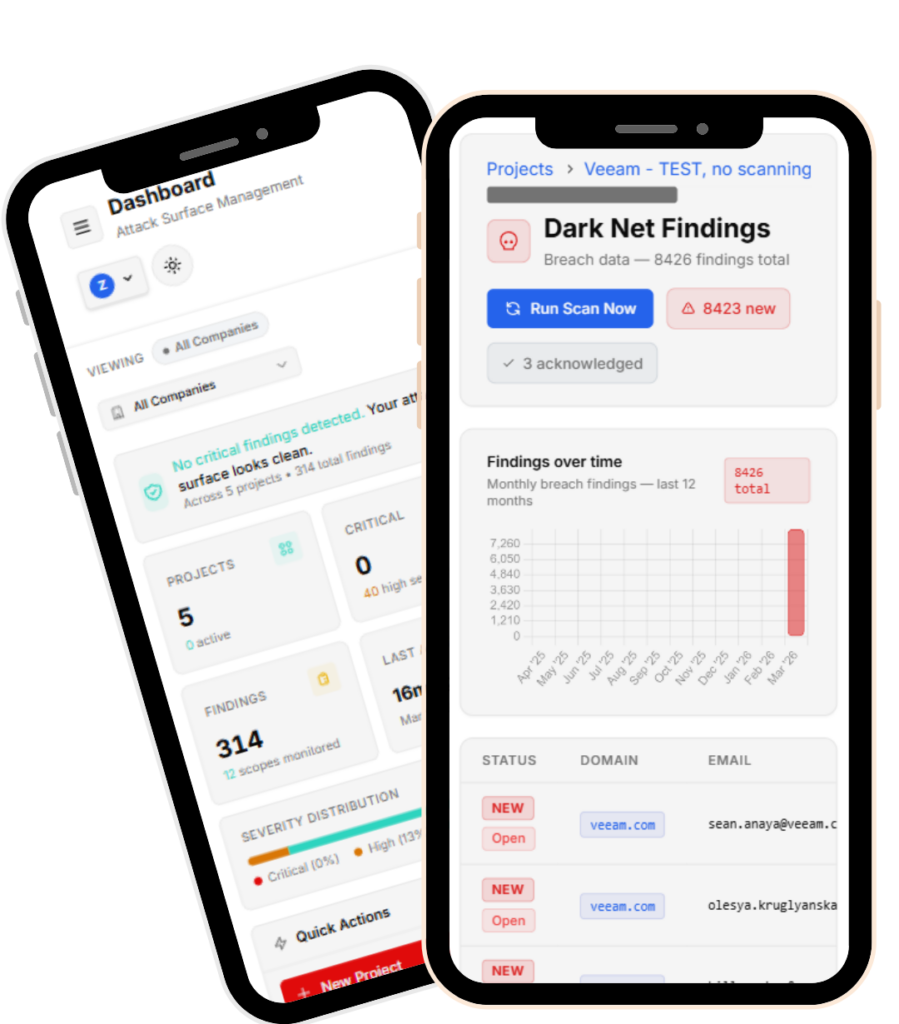
Analyze findings, understand the scope and evaluate the risk, all in just one page.
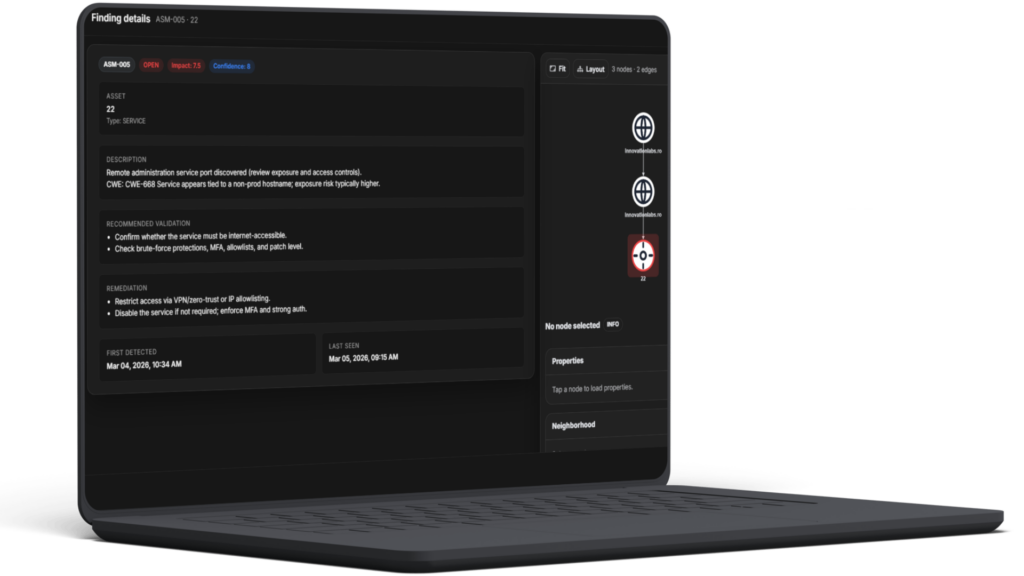
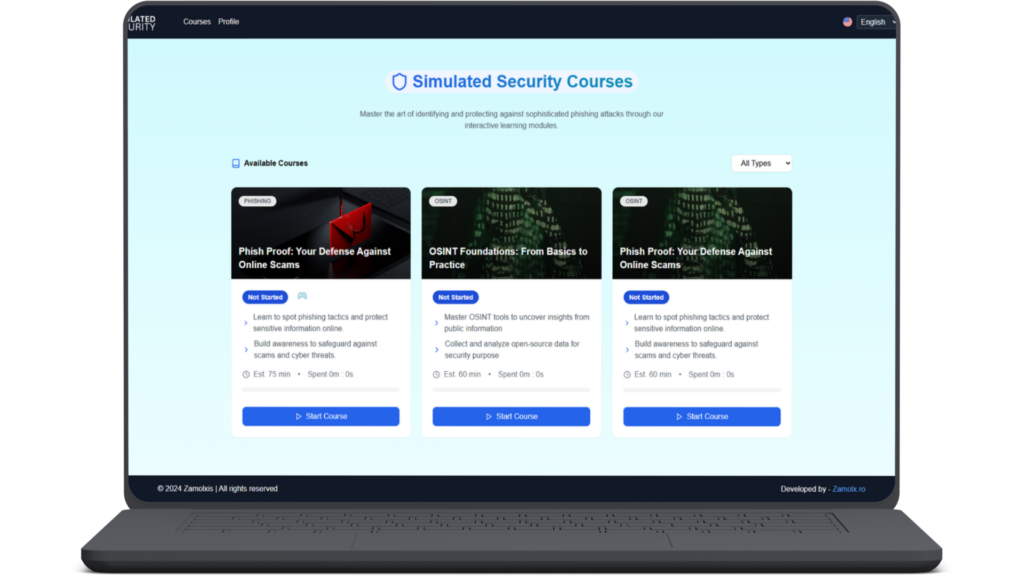
Train with a real attack simulator, fully emulated in a visual interface.
Efficiency. Visibility. Operativity.
Our platform empowers you to boost productivity without the hassle. With intuitive tools and seamless integrations, you can automate repetitive tasks and streamline workflows. Experience a smarter way to work, where achieving more feels effortless.
Embrace cutting-edge solutions that drive change and elevate your operations. Our platform enables you to harness innovation, streamline processes, and adapt to market demands, positioning your business for building real security.
Unlock the power of teamwork with our platform designed for seamless collaboration.

Together we achieve more by supporting each other through every challenge.

John Smith directs company strategy and for growth, innovation and team collaboration

John Smith directs company strategy and for growth, innovation and team collaboration

John Smith directs company strategy and for growth, innovation and team collaboration
Yes. Discovery and monitoring are designed to work without endpoint agents for fast deployment.
Yes. Use built-in connectors, webhooks, and an API-first approach for routing.
Evidence-backed findings and scoring aligned to exposure, exploitability, and ownership signals.
Yes. Map checks to your internal thresholds and enforce policies across business units.