Operational ASM from discovery to evidence to tickets
The modern enterprise no longer has a defined perimeter. Cloud migrations, remote work, and rapid deployments have created a sprawling digital footprint, inevitably leading to forgotten assets, misconfigurations, and shadow IT. These blind spots are exactly what adversaries look for.
Enumerate domains, hosts, services, technologies, and cloud exposure with continuous refresh.
Track new assets, config changes, and exposures. Trigger alerts and workflows when drift happens.
Monitor brand abuse, suspicious domains, typosquats, and impersonation. Automatically capture evidence, correlate infrastructure, and generate takedown-ready cases.
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book.
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book.
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book.
Visualize all assets, domains, IPs, services. Understand the infrastructure and acknowledge changes.
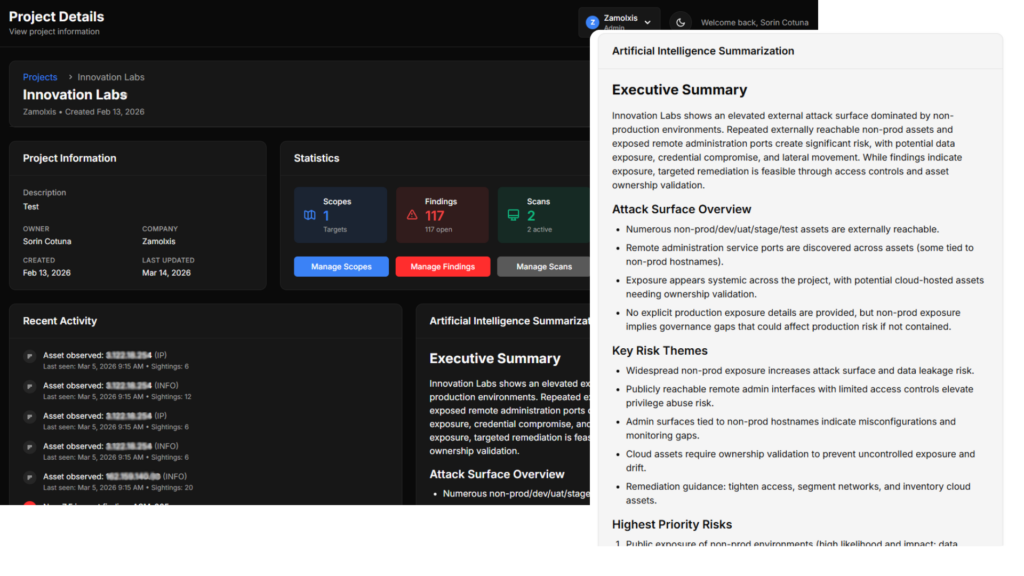
Assess the risks and model the threats. Compare risk scores and generate reports.
Schedule scans and monitor notifications within the integrated channels available.
Explore content across a variety of languages and ecosystems with interactions built directly into your Surface workflow.
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s
Yes. Discovery and monitoring are designed to work without endpoint agents for fast deployment.
Yes. Use built-in connectors, webhooks, and an API-first approach for routing.
Evidence-backed findings and scoring aligned to exposure, exploitability, and ownership signals.
Yes. Map checks to your internal thresholds and enforce policies across business units.