Cybersecurity platform built for operational defense. Automated attack surface discovery, dark web scanning, phishing simulations, and continuous monitoring work together to deliver military-grade protection against modern cyber threats.








As cyber threats evolve across multiple vectors - from exposed assets and misconfigurations to human vulnerability - traditional security tools alone are no longer enough. Our platform delivers a unified cybersecurity ecosystem designed to secure your digital footprint and eliminate critical visibility gaps.
By combining attack surface discovery, dark web intelligence, phishing simulations, and security training, we strengthen both technical defenses and human resilience. Built by security professionals, our military-grade technologies provide the insight and operational advantage needed to detect and neutralize modern cyber threats.
Transform security from a reactive bottleneck into a proactive strategic advantage.
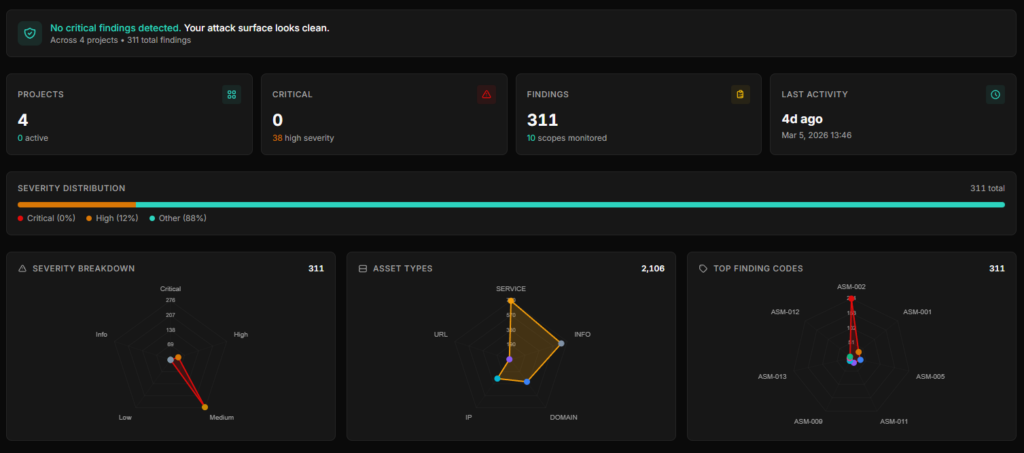
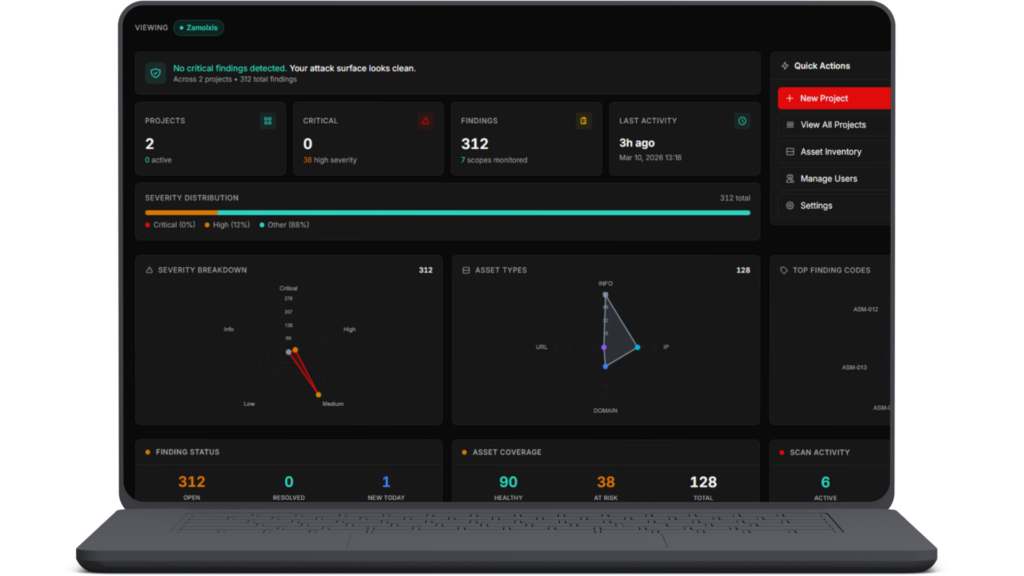
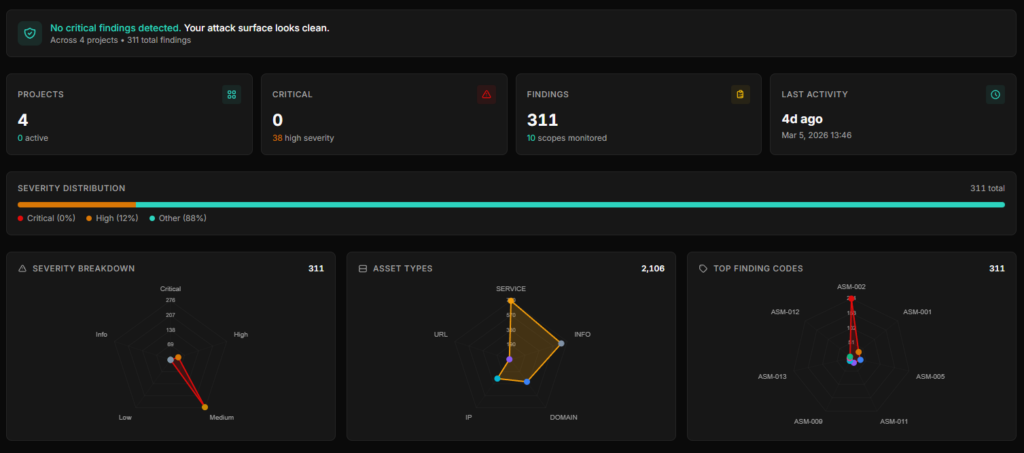
Gaining complete visibility over your digital footprint. We continuously map, score, and monitor every exposed asset – both known and unknown – before adversaries can exploit them.
Our platform is built on real-world hacker techniques, letting you simulate multi-step phishing attacks, 2FA bypass, QR exploits, Quishing, Vishing, and more – at scale – so your team trains against attacks they’ll actually face.
Go beyond quizzes and theory. Our platform delivers fully visual, real-world immersive scenarios that train your team to respond like seasoned operators. Fully automated but with the focus on measurable results – not just statistics.
Stay ahead of emerging threats with continuous dark web and OSINT monitoring. Identify leaked credentials, compromised assets, and hidden risks before adversaries can exploit them, turning intelligence into actionable defense.
Take full control over your human risk and attack surface from a single, uncompromising interface.
Simulate sophisticated phishing attacks tailored to your industry. Expose real human vulnerabilities before attackers do.
Replace boring, compliance-driven seminars with bite-sized, data-driven visually interactive trainings. We simulate real attacks inside web emulators and showcase practical methods to detect them.
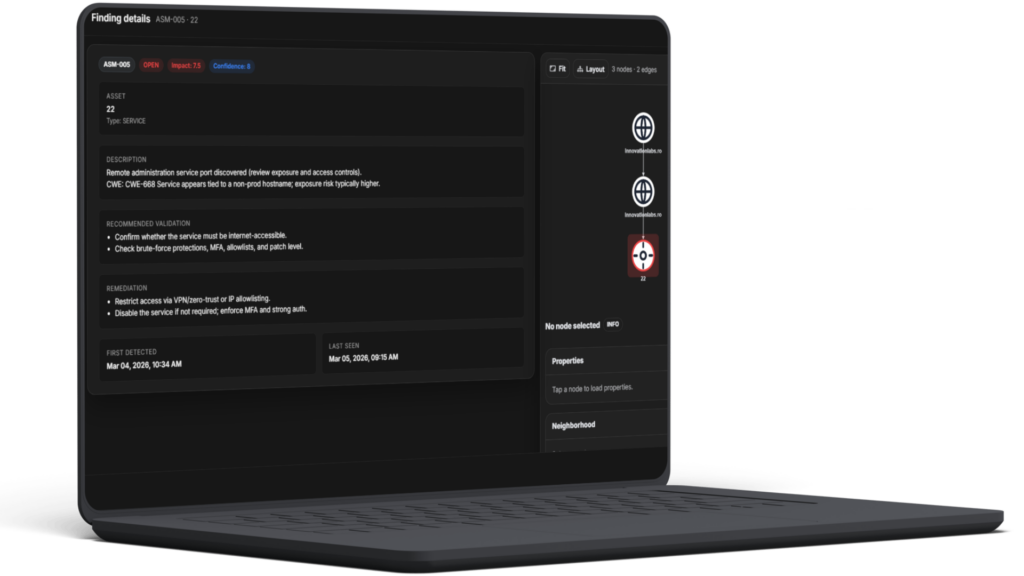
Your infrastructure is constantly shifting. Our ASM engine continuously maps your external footprint, uncovering shadow IT, forgotten subdomains, exposed services and leaked credentials in real-time.